Experimental Results
Comprehensive analysis across multiple scenarios and noise conditions
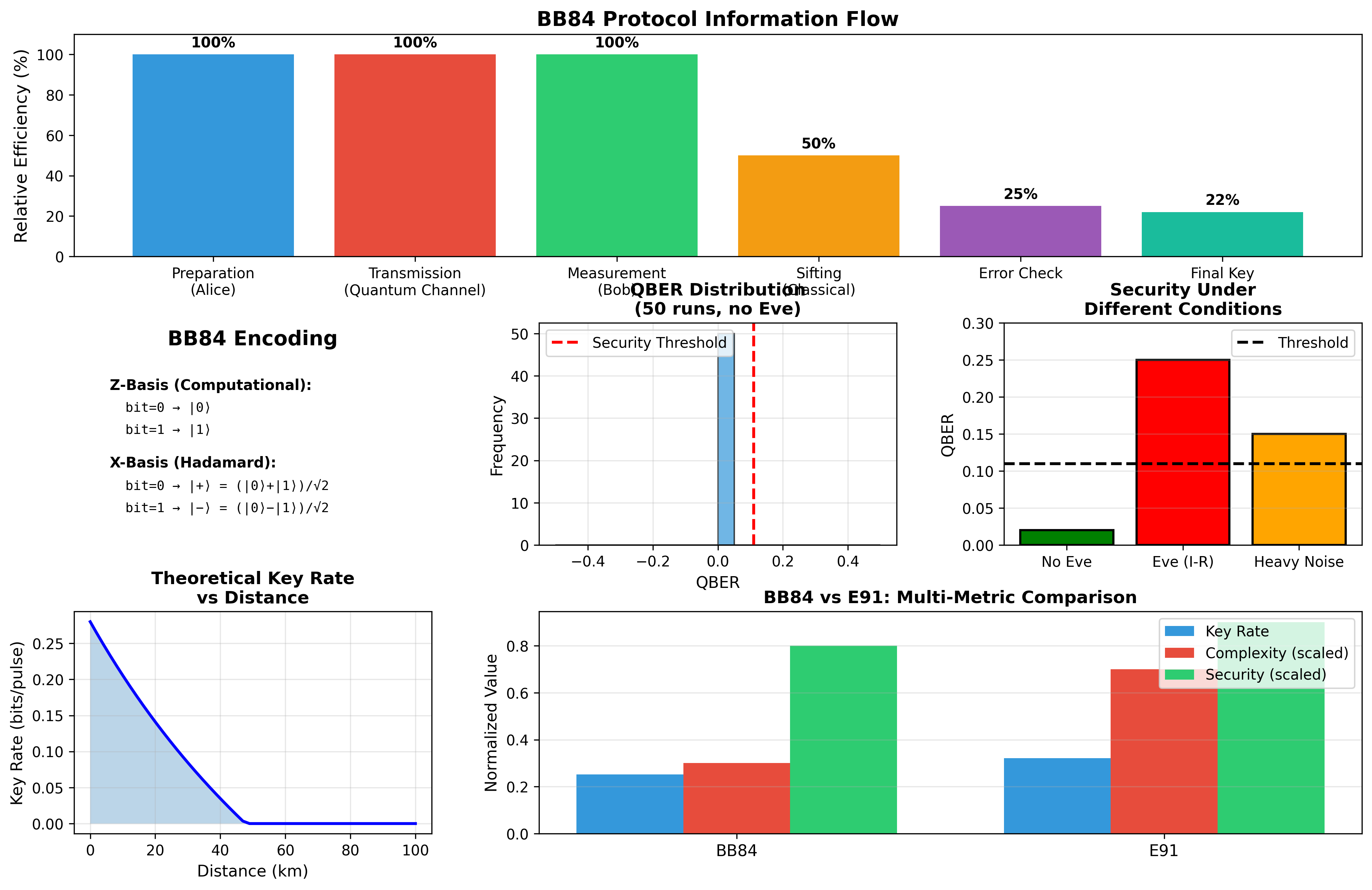
Protocol Workflow & Information Flow
Visualization of the complete BB84 protocol stages showing efficiency degradation from preparation (100%) through final key generation (22%). The sifting phase reduces bits by 50% due to basis matching, while error checking and privacy amplification further compress the key.
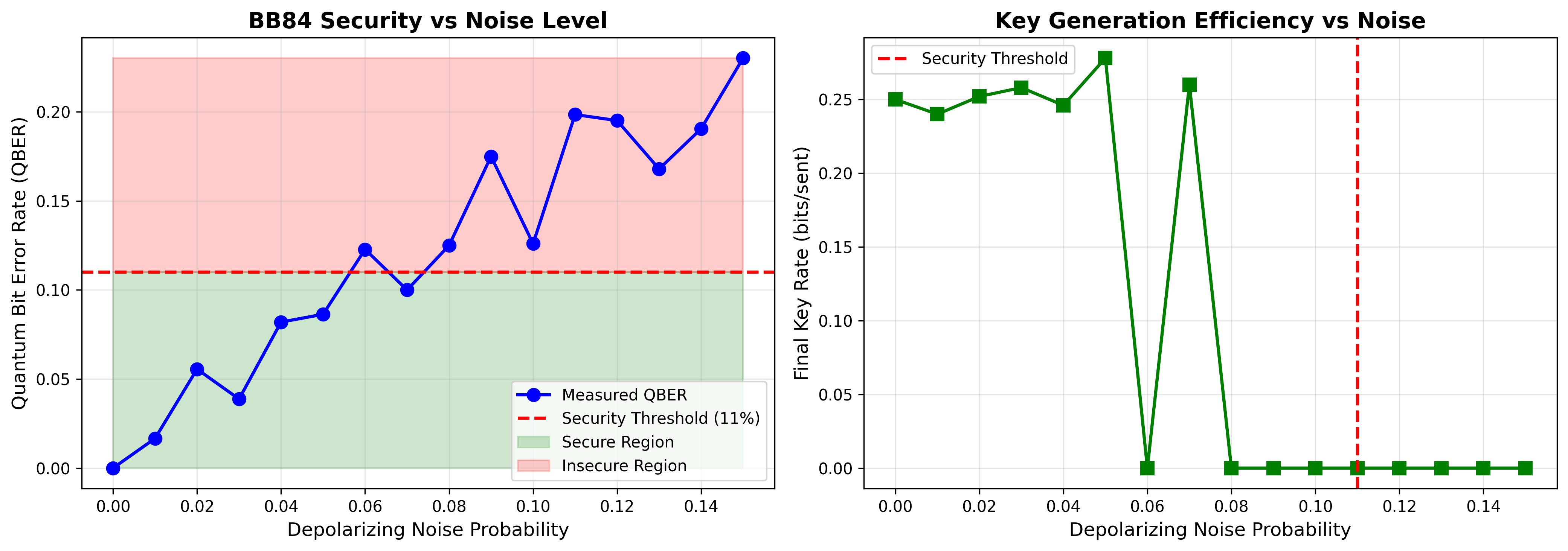
Noise Tolerance & Security Threshold
Analysis of BB84 performance under varying depolarizing noise levels from 0% to 15%. The protocol maintains security below the 11% QBER threshold (green region), with key generation rate degrading gracefully as noise increases. Above the threshold (red region), the protocol correctly aborts to prevent compromised key usage.
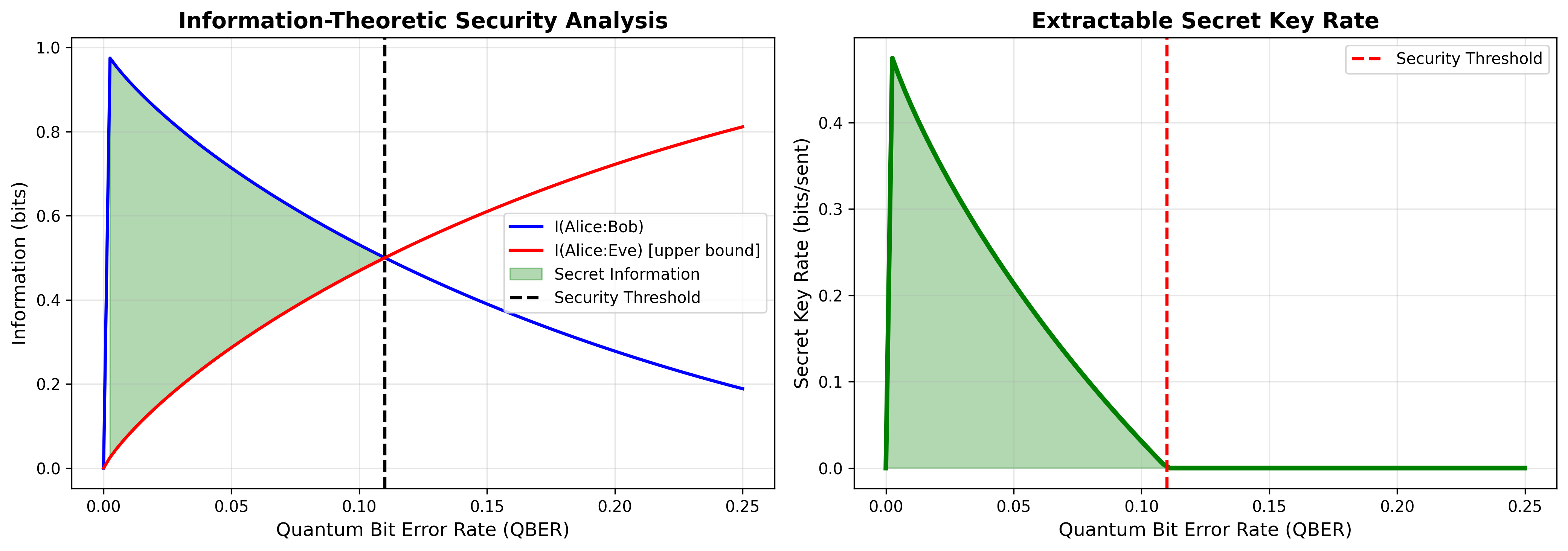
Information-Theoretic Security Analysis
Shannon mutual information curves demonstrating the security foundation of BB84. The green shaded region represents extractable secret information where I(Alice:Bob) exceeds I(Alice:Eve). At QBER = 11%, mutual information converges to zero, defining the theoretical security threshold. Secret key rate calculation accounts for sifting efficiency and privacy amplification overhead.
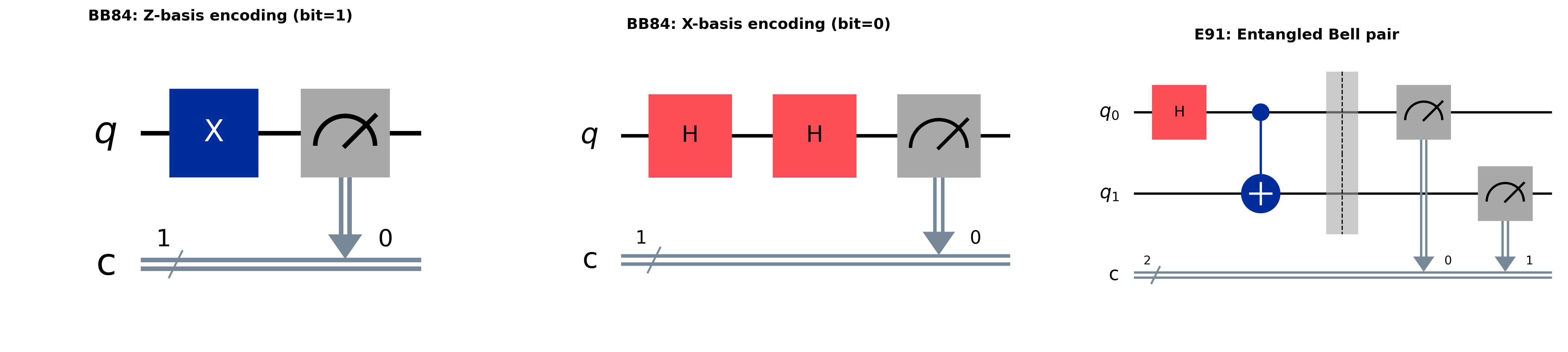
Quantum Circuit Examples
Representative quantum circuits for BB84 encoding schemes and E91 entanglement generation. Left: Z-basis encoding with X gate for bit=1. Center: X-basis encoding with double Hadamard transformation. Right: Maximally entangled Bell state |Φ+⟩ = (|00⟩ + |11⟩)/√2 for E91 protocol with barrier separating preparation from measurement.
Performance Metrics Summary
| Scenario | QBER | Key Rate (bits/sent) | Final Key Length | Secure? |
|---|---|---|---|---|
| Clean Channel | 0.000 | 0.251 | 53 bits (from 200 sent) | ✓ Yes |
| With Eavesdropper (I-R) | 0.230 | 0.000 | 0 bits (protocol aborted) | ✗ No |
| Low Noise (2%) | 0.035 | 0.254 | ~50 bits (from 200 sent) | ✓ Yes |
| High Noise (8%) | 0.116 | 0.114 | ~23 bits (from 200 sent) | ✓ Yes |
✓ Key Findings
- Eavesdropping Detection: